Key Generation Algorithm In Cryptography
Cryptography
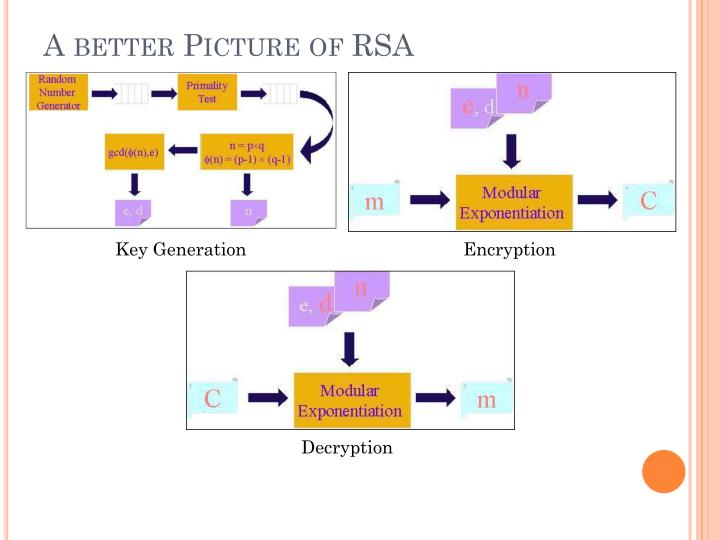
There are many encryption algorithms for the public keys. The two main ones are the RSA system of cryptography and the Elliptic Curve Cryptography. We will focus on this last algorithm since it is the system which has been adopted by the Bitcoin Protocol. The RSA is the first system to have been used in the framework of the public key encryption and remains today the most used. In Cryptography, the Key Generation is the process of generating Keys with the help of algorithms. Keys are being used to encrypt and decrypt the communication, information, and data. A Key Generator Software or The Web Tool is being used to gener. The key may be a private key or a public key. Asymmetric-key algorithm A cryptographic algorithm that uses two related keys, a public key and a private key. The two keys have the property that determining the private key from the public key is computationally infeasible. Also known as a public-key algorithm. Symmetric key. In this type of cryptography both the parties (sender and receiver) use same key to encrypt and decrypt the message. A popular symmetric key algorithm is Data Encryption Standard (DES), there are also its modern variants such as Triple DES. Asymmetric key. In this type, there are two keys, public and private. The Quantum Key Factory is a platform which allows for a combination of multiple sources of randomness (entropy), as well as best practice key scheduling, key mixing, key storage and key auditing to guarantee secure key generation at the highest level of trust. True random number generation platforms based on Quantis QRNG. RSA Function Evaluation: A function (F), that takes as input a point (x) and a key (k) and produces either an encrypted result or plaintext, depending on the input and the key. Key Generation The key generation algorithm is the most complex part of RSA. The aim of the key generation algorithm is to generate both the public and the private.
Derrick Rountree, in Security for Microsoft Windows System Administrators, 2011
That generates a 2048-bit RSA key pair, encrypts them with a password you provide and writes them to a file. You need to next extract the public key file. You will use this, for instance, on your web server to encrypt content so that it can only be read with the private key. Export the RSA Public Key to a File. This is a command that is. Openssl rsa -in private.pem -outform PEM -pubout -out public.pem.  If you use ssh-keygen to generate a key: $ ssh-keygen Then you can just use openssl to pull out the public key and write it in the DER format like this: $ openssl rsa -in idrsa -out pub.der -outform DER -pubout writing RSA key You can view the DER output as PEM like this: $ openssl rsa -in pub.der. Run 'openssl genrsa' to generate a RSA key pair. Run 'openssl req -new -x509' to generate a self-signed certificate and stored it in PEM format. Run 'openssl x509' to convert the certificate from PEM encoding to DER format. The test session was recorded below.
If you use ssh-keygen to generate a key: $ ssh-keygen Then you can just use openssl to pull out the public key and write it in the DER format like this: $ openssl rsa -in idrsa -out pub.der -outform DER -pubout writing RSA key You can view the DER output as PEM like this: $ openssl rsa -in pub.der. Run 'openssl genrsa' to generate a RSA key pair. Run 'openssl req -new -x509' to generate a self-signed certificate and stored it in PEM format. Run 'openssl x509' to convert the certificate from PEM encoding to DER format. The test session was recorded below.
Cryptographic key (key) A parameter used in conjunction with a cryptographic algorithm that determines its operation in such a way that an entity with knowledge of the correct key can reproduce or reverse the operation, while an entity without knowledge of the key cannot. Examples of cryptographic.
Asymmetric Encryption
Asymmetric encryption is also referred to as public key encryption. In asymmetric encryption, both the encrypting and decrypting systems have a set of keys. One is called the public key, and another is called the private key. If the message is encrypted with one key in the pair, the message can be decrypted only with the other key in the pair.
Asymmetric key algorithms are not quite as fast as symmetric key algorithms. This is partially due to the fact that asymmetric key algorithms are generally more complex, using a more sophisticated set of functions.
Asymmetric Key Algorithms
Comparing Cryptography Algorithms
Asymmetric key algorithms aren't as widely used as their symmetric counterparts. So we'll just go over two of the big ones: Diffie-Hellman and RSA.
Diffie-Hellman: The Diffie-Hellman algorithm was one of the earliest known asymmetric key implementations. The Diffie-Hellman algorithm is mostly used for key exchange. Although symmetric key algorithms are fast and secure, key exchange is always a problem. You have to figure out a way to get the private key to all systems. The Diffie-Hellman algorithm helps with this. The Diffie-Hellman algorithm will be used to establish a secure communication channel. This channel is used by the systems to exchange a private key. This private key is then used to do symmetric encryption between the two systems.
RSAConstruct 2 key generator torrent. : It is the Rivest Shamir Adelman algorithm. RSA was developed in 1978. RSA was the first widely used asymmetric algorithms used for signing and encryption. It supports key lengths of 768 and 1,024 bits. The RSA algorithm uses a three-part process. The first part is key generation. The keys used in the RSA algorithm are generated using mathematical operations based on prime numbers. The second part of the process is encryption. This encryption is done using one of the keys in the key pair. The third part of the process is decryption. The decryption is done using the other key in the key pair.
Read full chapter